
An organization's data strategy will not be complete without a Data Architect. This role is responsible for standardizing the way organizations store, transform, and use their data. They typically combine business and technical skills. But data architects have some special skills that are highly desirable. If you want to become one of these individuals, read on to discover what makes a great data architect. These are essential skills that a Data Architect must have.
Data architecture is at the heart of any data strategy
An enterprise data structure can enhance communication and collaboration in an organization. A data architecture can help an enterprise to reap the benefits and avoid silos within its organization. Data integration can ease the burden of developers by keeping data in a consistent format so that everyone can use the same version. By using an enterprise data architecture, an enterprise can leverage data from multiple sources, enabling data scientists to create more effective and efficient analytical applications.
To develop a data architecture, it is necessary to have a deep understanding of each component and their role within the data environment. Data security is an essential component of any data architecture. It should always be considered. Best practices should be followed throughout the development process, from initial design concepts to infrastructure deployment and day-to-day operations, to ensure that everyone understands their responsibilities. Data architectures can only work if all parts are in sync.
It's the standardization of how organisations collect, store and transform data.
Data management and effective data use requires organizations to identify and document all their data. It's much easier to manage and distribute the data when it is all organized in one place. It is also important to avoid repeating the same data collection. Metadata such as taxonomic and vocabularies help organizations to identify and manage their data. This ensures that no one is attempting to duplicate their efforts.
Modern data architecture employs machine learning and artificial Intelligence to standardize and automate the collection, transformation and distribution of data. Machine learning and artificial intelligence are able to identify data types and error, suggest solutions and alert users about new situations. Machine learning can also identify relationships among data sets and provide fresh insights. Machine learning can also suggest related data sets which will allow data scientists make faster and easier decisions.
This requires creative problem solvers and analytical skills.
A data architect is highly skilled. They should be able to analyze data and communicate business insights. Coding errors can result in millions of dollars being lost. These people must be meticulous. Data architects need to be problem solvers and have strong analytical skills. Flexible and able to meet deadlines are essential qualities for a data architect. You will need to be able to think outside the box to find creative solutions to business problems.
Big data is essential for creative and analytical people. IT has seen a lot of short-term thinking, which leaves little room for quality, governance, and serving the business. Both users and businesses both want things done fast, but it's important that we balance these needs. Both skills are required for data architects. Here are some skills needed to become a Data Architect.
It requires both technical and business skills.
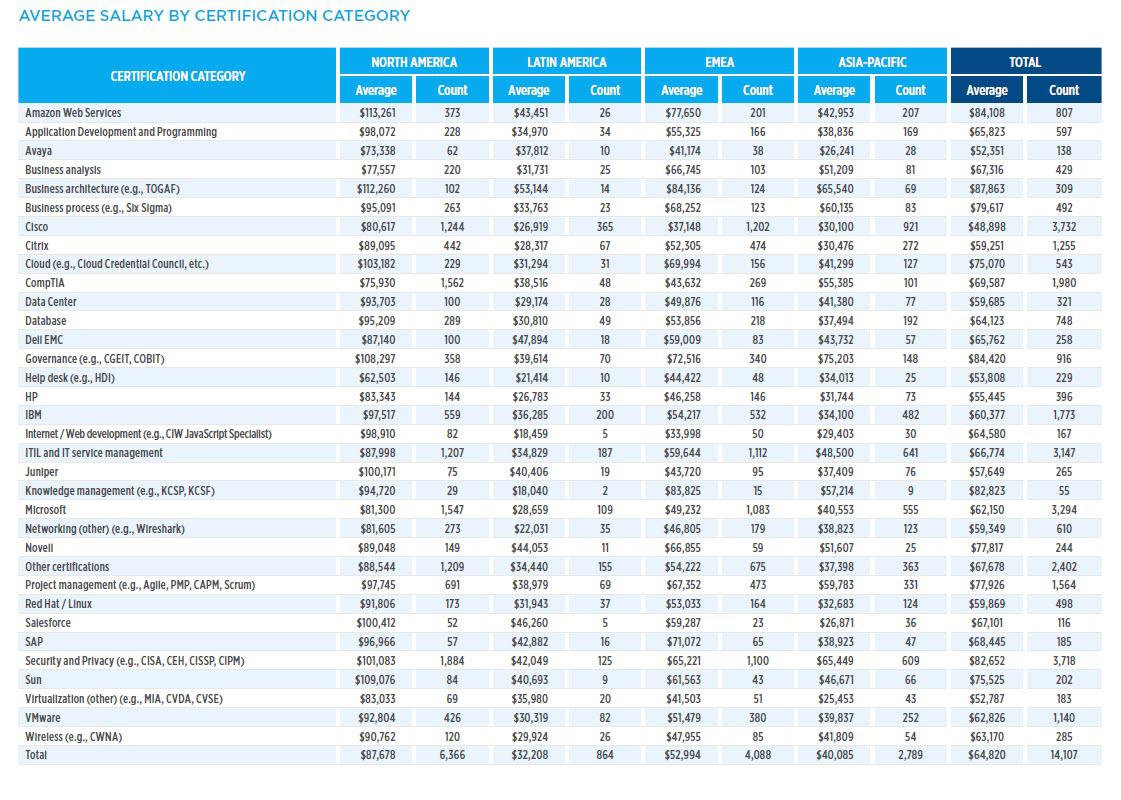
Architects in this role need to be adept at managing a team and advising them in the right direction. They should be proficient in all aspects of the industry, as well as a sound understanding of data management principles and data modelling. These skills can also be developed through additional training and certifications. Salesforce, Hortonworks, IBM and Hortonworks certifications are great for expanding one's understanding of data architecture.
Data architects bridge the gap between IT operations and business operations. He/she must ensure that data are stored and retrieved securely while complying with regulations. The responsibilities of this role are often broad in scope, covering both data storage and management. In addition to working with business and IT managers, data architects also work closely with key team leaders and managers and play a key role in the development and implementation of applications.
It requires certification
Data architects must be well-versed in the data industry and be up to date with technological developments. Many data professionals are required to be proficient in data visualization. This is the art of presenting data visually. There are various tools and resources available to make data visualization more attractive. Here are some examples. This certification will increase your skill set. These tips will help you to consider getting one. However, before you can apply for the certification you need to be familiar with the job requirements.
Data architecture professionals need to be certified. This certification can increase the salary of professionals and open up doors. There are many professional certifications that you can take depending on the area of your expertise. This will allow you to improve your knowledge and give you an advantage in the industry. The Certified Data Management Professional (CDMP) is the most popular certification in data architecture. The CDMP requires two years' experience and a bachelor’s degree. Anyone who is interested in working in database management should consider a CDMP.
FAQ
What should I look out for when selecting a course in cyber security?
There are many types of cyber security courses, from short courses to long-term programs. Here are some things to consider when choosing the right one. These are some ideas to consider:
-
What level certification would you prefer? Some courses provide certificates upon successful completion. While others offer diplomas, or degrees. Although certificates are usually easier to obtain than degrees, diplomas or degrees are generally more prestigious.
-
How many weeks/months will you be able to finish the course? Courses typically last 6-12 weeks. Some courses may take longer.
-
Do you prefer face-to–face interaction or distance-learning? Although face-to–face courses can be great for making friends and getting to know others, they can be quite expensive. Distance learning lets you work at your own pace while saving money on travel expenses.
-
Are you looking for career changes or a refresher? Some career changers may not have the time or desire to change their job. Others might find that a quick course will suffice to refresh and improve their skills. Others might simply want to refresh their knowledge before applying for a job.
-
Is it accredited? Accreditation assures that a course's reliability and credibility. Accreditation ensures you won’t waste your money and time on courses that don’t deliver the results that you are looking for.
-
Are there internships available? Internships give you the opportunity to apply what's been learned and work with IT professionals. Placements offer you the chance to learn from cybersecurity experts and get valuable hands-on experience.
How long is a Cyber Security Course?
Cybersecurity training courses typically last between six and 12 weeks, depending on how much time you have available for study. If you're looking for a shorter-term course, you might want to look into an online option like the University of East London Cyber Security Certificate Program. This program meets three times per weeks over four consecutive week. Or, you could opt to take the full-time immersive version if your time is limited. These include classroom lectures, assignments, group discussions, and group discussions. All of these are designed to provide a solid foundation in cybersecurity. The tuition fee covers everything, including accommodation, meals, textbooks, and IT equipment; this makes it easy to budget. Along with learning the basics of cybersecurity from scratch students also learn practical skills such a penetration testing, network security, ethical hacking, incident response and cryptography. After completing the course, students receive a certificate. As well as helping people get started with their careers in cybersecurity, the program has helped hundreds of students secure jobs in the industry after they graduate.
A shorter course can be finished in two years. That's the best part. But if you are looking for long-term training, it will probably take you more time. Of course, you will spend most of your time studying, but you will also have to attend regular classes. An extended course will cover topics such vulnerability assessment, mobile device management, digital encryption, digital forensics, and malware. If you choose to take this route, you'll need to devote up to six hours per day to your studies. Regular attendance at scheduled meetings will be a requirement, whether they are in person or via online platforms like Skype or Google Hangouts. These may be mandatory depending on where you live.
Course duration will depend on whether you choose a full-time or part-time program. Part-time courses tend to last less than full-time programs, so you might not be able to see the entire curriculum. Full-time programs are more intense and will therefore likely be spread over multiple semesters. Whatever your choice, make sure your course has flexible scheduling options that allow you to fit it in your busy schedule.
What will be the future trends in cybersecurity technology?
The security industry is constantly evolving at an unimaginable rate. New technologies are emerging, old ones are getting updated, and existing ones are becoming obsolete. The threats we face also change constantly. Our experts will provide you with an overview of current events and deep dives into recent developments.
You will find everything here.
-
The most recent news on attacks and vulnerabilities
-
Solutions that work best for the latest threats
-
Guide to staying ahead
The future holds many opportunities. There is no way to know what lies beyond. Therefore, we can only hope for luck and plan for the next few decades.
However, if you really want to know what the future holds, then all you need to do is read the headlines. They say that hackers and viruses don't pose the greatest threat. Instead, it's governments.
All governments around the globe are constantly trying to spy on their citizens. They use advanced technology (including AI) to monitor activity online and track people's movements. They collect data from anyone they come across in order to build detailed profiles on individuals and groups. To them, privacy doesn't exist because they see it as nothing more than a hindrance to national security.
The power is being used by the government to target particular individuals. Experts think that the National Security Agency might have already used its powers for influence in Germany and France's elections. It is not clear if the NSA intentionally targeted these countries but it does make sense if we think about it. You need to ensure that the population doesn't stand in your path if you want control over them.
This isn’t a hypothetical scenario. History has shown that dictatorships often hack into opponents' phones and steal their data. It seems as though there are no limits to what governments will do in order keep their subjects under control.
You might still be worried about corporate spying, even though you don't worry about surveillance at the federal level. There's no evidence that big businesses may be tracking your every move online. Facebook tracks your browsing history, regardless of whether or not you have given permission. And while Google claims it doesn't sell your data to advertisers, there's no proof of that either.
It is important to not only be concerned about the consequences of government involvement, but also to think about how you can protect yourself against corporate intrusions. For those who work in IT, cybersecurity is something you need to be aware of. It could also help to prevent sensitive information from being accessed by companies. You could also teach employees how to spot potential phishing schemes and other forms of social engineering.
Cybercrime is a major problem currently facing society. Cybercriminals, hackers, criminals and terrorists are constantly working together to steal and damage your personal data. There are solutions for every problem. All you need to do is find out where to start looking.
Statistics
- The top five regions contributing to the growth of IT professionals are North America, Western Europe, APJ, MEA, and Central/Eastern Europe (cee.com).
- The top five countries contributing to the growth of the global IT industry are China, India, Japan, South Korea, and Germany (comptia.com).
- The global IoT market is expected to reach a value of USD 1,386.06 billion by 2026 from USD 761.4 billion in 2020 at a CAGR of 10.53% during the period 2021-2026 (globenewswire.com).
- The IT occupation with the highest annual median salary is that of computer and information research scientists at $122,840, followed by computer network architects ($112,690), software developers ($107,510), information security analysts ($99,730), and database administrators ($93,750) (bls.gov).
- The median annual salary of computer and information technology jobs in the US is $88,240, well above the national average of $39,810 (bls.gov).
- The United States has the largest share of the global IT industry, accounting for 42.3% in 2020, followed by Europe (27.9%), Asia Pacific excluding Japan (APJ; 21.6%), Latin America (1.7%), and Middle East & Africa (MEA; 1.0%) (comptia.co).
External Links
How To
How do I start learning cyber security?
People who have been involved with computer technology since a very young age are likely to be familiar with hacking. This may be confusing for some.
Hacking refers primarily to the use of viruses, trojans or spyware to gain unauthorised access computers, networks and other systems.
Cybersecurity is now a major industry that offers ways to defend against attacks.
You need to understand the workings of hackers to better understand how you can stay safe online. To help you begin your journey toward becoming more informed about cybercrime, we've compiled some information here:
What is Cyber Security?
Cyber security means protecting computers from external threats. Hacking your system can give someone access to your files, money or other information.
There are two types in cybersecurity: Computer Forensics, and Computer Incident Response Teams.
Computer forensics involves the analysis of a computer in response to a cyber attack. It's done by experts who search for evidence that will lead them to the attacker responsible. Computers are examined for signs of tampering and damage caused by viruses or malware.
The second type of cybersecurity is CIRT. Teams of CIRT professionals work together to respond and prevent computer-related incidents. They use their expertise to stop attackers before they do significant harm.